OpenAI Enforces Advanced Account Security for ChatGPT
Breaking security upgrade: OpenAI has rolled out Advanced Account Security (AAS) — a zero-trust authentication model that disables passwords, removes email/SMS recovery, and mandates hardware security keys or passkeys.
🔐 What Is Advanced Account Security (AAS)?
On April 30, 2026, OpenAI launched Advanced Account Security, a hardened authentication framework designed for users managing sensitive workflows inside ChatGPT — including codebases, client data, automated agents (e.g., Codex), and private business intelligence.
Unlike traditional two-factor authentication (2FA), AAS operates on a phishing-resistant, cryptographic identity model — aligning with FIDO2/WebAuthn standards.
✅ Key Features
- Passwordless login — passwords are fully disabled.
- Mandatory passkey or physical security key (e.g., YubiKey) for all sign-ins.
- No email or SMS account recovery — replaced by backup passkeys, security keys, and cryptographically generated recovery keys.
- Automatic exclusion from model training — all conversations are opt-out-by-default for training.
- Shortened session lifetimes, real-time login alerts, and full visibility into active devices.

▲ Official OpenAI post — 175K views, 1.7K+ upvotes
⚠️ The Trade-Off: Maximum Security, Zero Recovery Safety Net
OpenAI explicitly states:
“OpenAI Support will not be able to assist with account recovery for users enrolled in Advanced Account Security.”
This means:
– If you lose your primary security key and fail to back up your recovery key or secondary passkey → permanent account lockout.
– No customer service escalation, no manual override, no exception.
As reported by TechCrunch:
“If the key is lost, OpenAI won’t be able to help recover access.”

▲ TechCrunch highlights OpenAI’s partnership with Yubico and strict recovery policy
🛡️ Beyond Login: End-to-End Session Hardening
AAS doesn’t stop at authentication — it secures the entire session lifecycle:
- Short-lived sessions: Automatic re-authentication required after defined idle periods.
- Real-time device monitoring: View and terminate suspicious active sessions instantly.
- Cross-device login notifications: Immediate alerts on new sign-ins across platforms.
- Privacy-first default: All AAS-enabled conversations are excluded from training datasets — no opt-in needed.
Additionally, Codex and other AI agent integrations inherit AAS protections, transforming ChatGPT from a chat interface into a secure AI workbench.
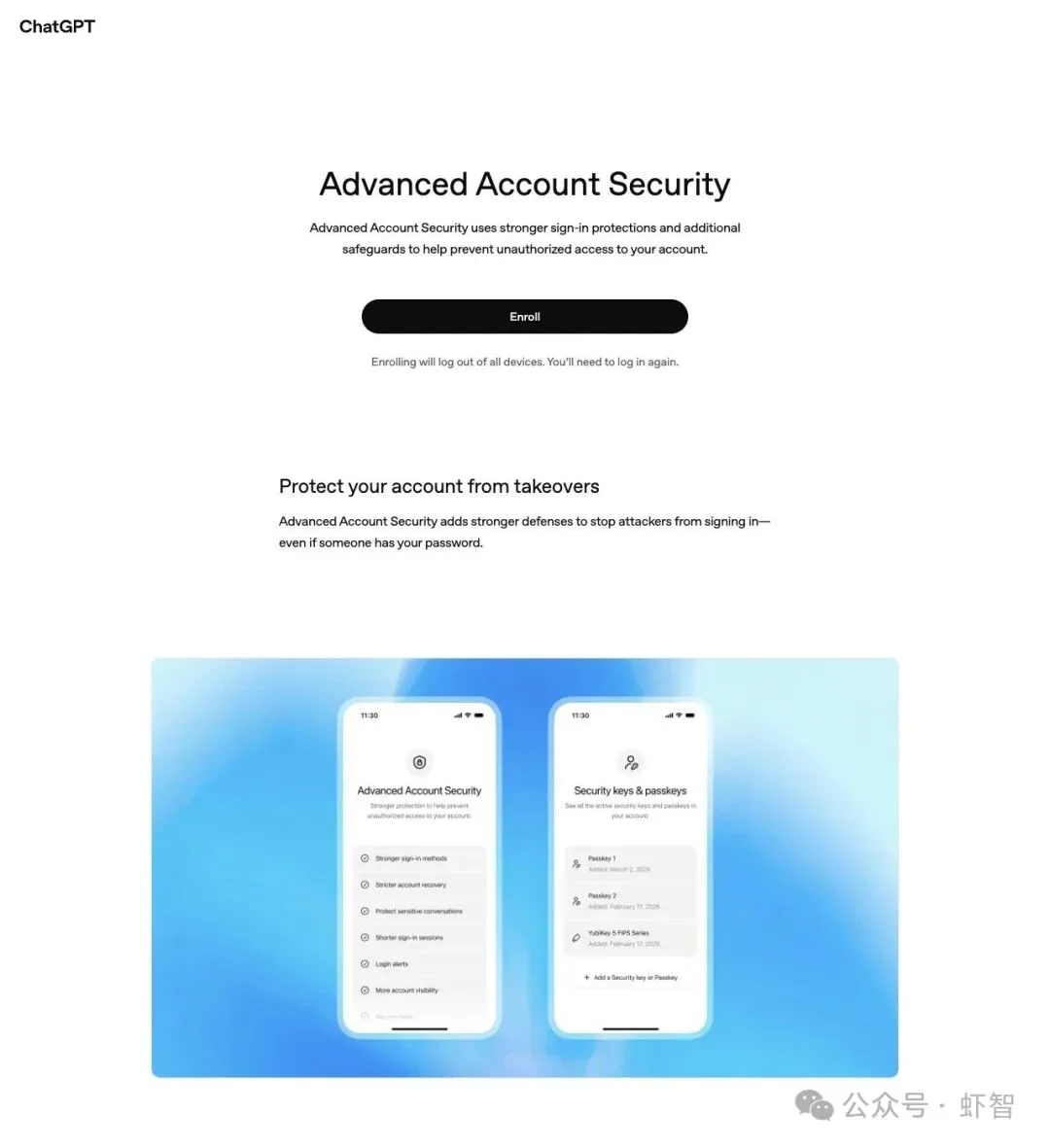
▲ Official AAS settings page: unified controls for login, recovery, and privacy
🤝 Official Partnership: OpenAI × Yubico
To lower adoption barriers, OpenAI partnered with Yubico, a leader in FIDO-compliant hardware security, to launch an official co-branded kit:
- YubiKey C NFC — supports tap-to-authenticate on smartphones and tablets.
- YubiKey C Nano — ultra-compact USB-C form factor, ideal for permanent laptop integration.
Jerrod Chong, CEO of Yubico:
“Ultimately, our intent is to drastically reduce the threat of unauthorized access to sensitive data in OpenAI accounts worldwide.”Dane Stuckey, OpenAI CISO:
“We’ve made YubiKeys a standard part of how we protect OpenAI employees…”

▲ Joint announcement: industry-first anti-phishing hardware bundle
💬 Community Reaction: Praise, Concerns & Critical Questions
The official announcement sparked over 1,200+ comments. While consensus favors the security direction, two major critiques dominate:
❓ 1. Why Not Default-Enabled?
“Truly high-risk users — journalists, activists, dissidents — often don’t know they’re targets. Security shouldn’t be opt-in; it should be the baseline.”
— @PodClipVibe
❓ 2. What About Post-Login Threats?
“Phishing resistance solves auth — but what about session hijacking, browser exploits, or token theft? AAS doesn’t cover endpoint compromise.”
— @orskyai
📅 Enforcement Timeline: Mandatory for Trusted Users Starting June 1, 2026
- June 1, 2026: AAS becomes mandatory for all individuals enrolled in Trusted Access for Cyber.
- Organizations must demonstrate phishing-resistant SSO (e.g., Okta + WebAuthn) to comply.
This signals OpenAI’s shift toward tiered security architecture, where AAS serves as the foundational layer for enterprise-grade trust.
🧭 Final Perspective: Security Is a Choice — Not Just a Feature
OpenAI’s move reflects a broader evolution: ChatGPT accounts are no longer casual logins — they’re gateways to AI-powered workstreams.
- For developers, researchers, and professionals handling confidential assets: AAS offers unmatched protection.
- For general users: The trade-off — irreversible lockout vs. enhanced resilience — demands careful key management.
As OpenAI affirms:
“We’d rather make it harder to get in — than easier for attackers to stay in.”
Source: Original reporting by “Xia Zhi” via WeChat Official Account.