Claude Code Source Code Leak Exposed via npm Source Map
Breaking Security Incident — On March 31, 2026, security researcher Chaofan Shou discovered that Anthropic’s Claude Code source code was fully exposed on the public npm registry through an unfiltered source map file.
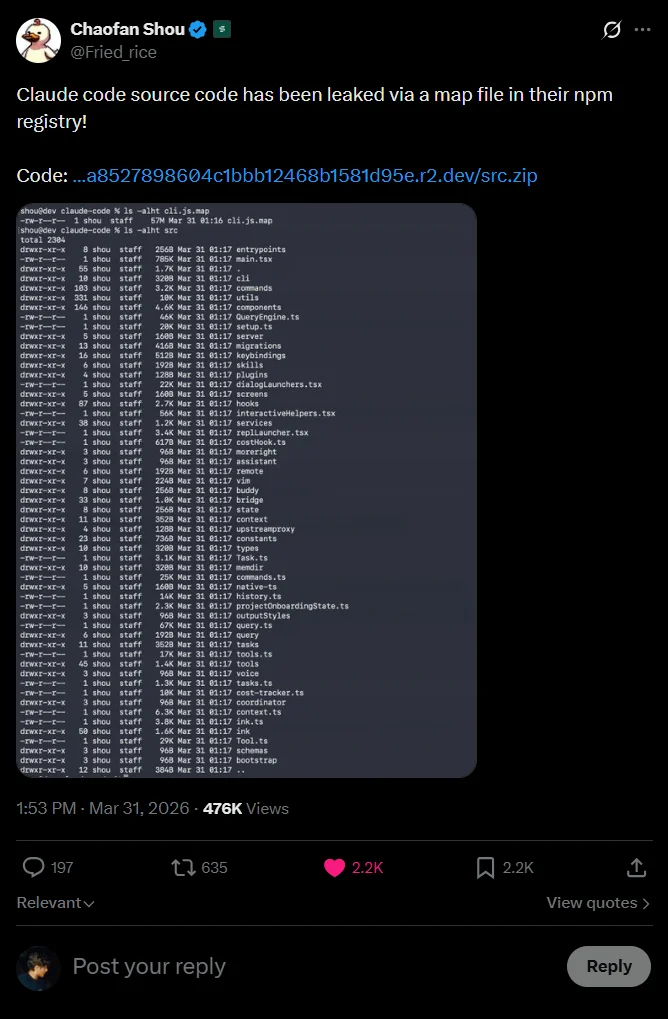
Chaofan Shou announced the leak on X
Full Code Exposure: Scale & Scope
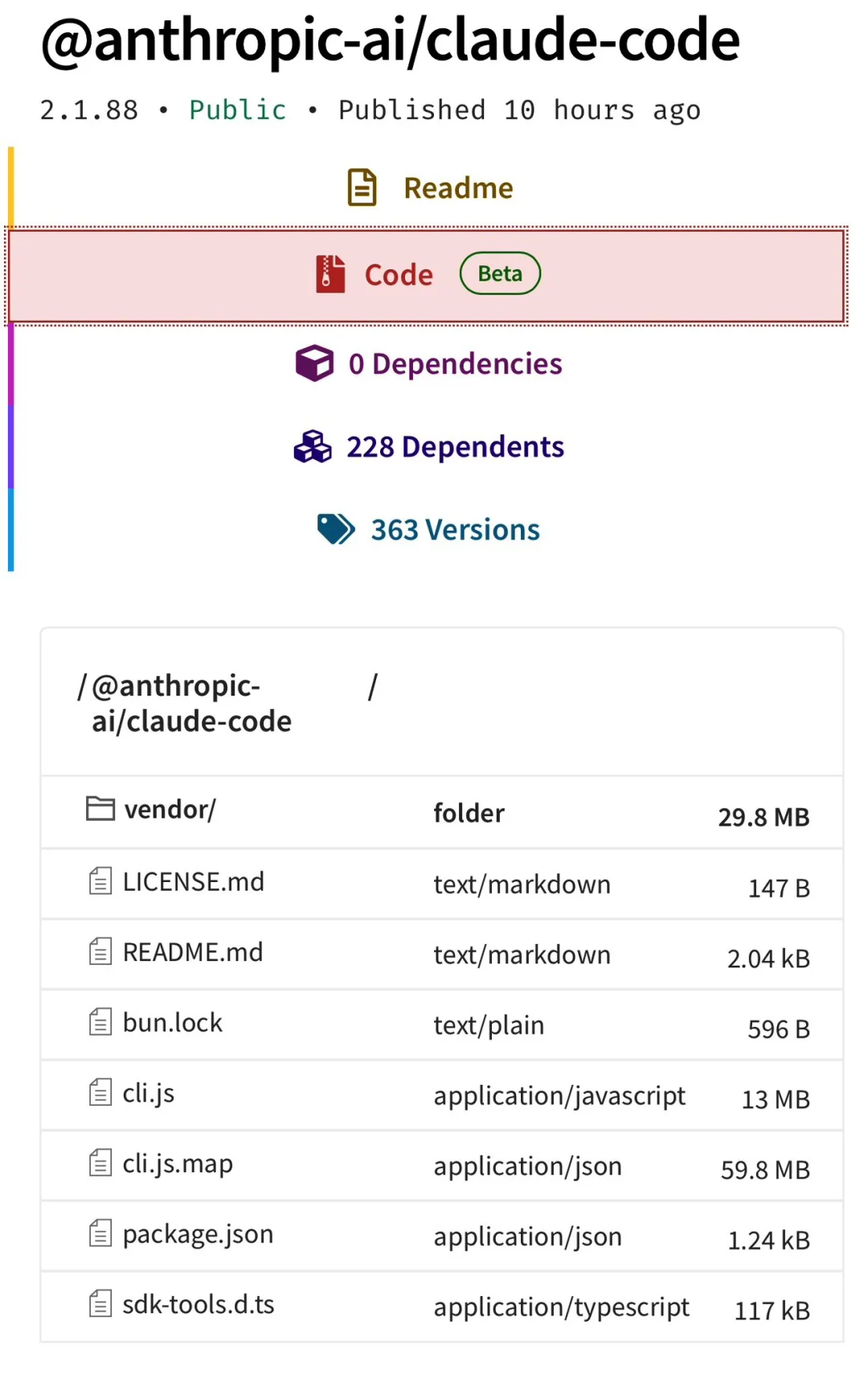
The leaked package — @anthropic-ai/claude-code v2.1.88 — contained:
- ✅ 1,900 TypeScript source files
- ✅ 512,000 lines of unobfuscated, production-grade code
- ✅ Complete architecture — from tooling and permissions to unreleased features like KAIROS, ULTRAPLAN, and Buddy
- ✅ A 59.8 MB
.mapfile, inadvertently published due to misconfigured Bun build pipeline
Within hours, the code was mirrored across GitHub. The largest backup repository — instructkr/claude-code — surged to:
- ⭐ 11,300+ stars in under one hour
- 🍴 17,300+ forks (exceeding star count — signaling mass archival)
- 🐞 568 open issues
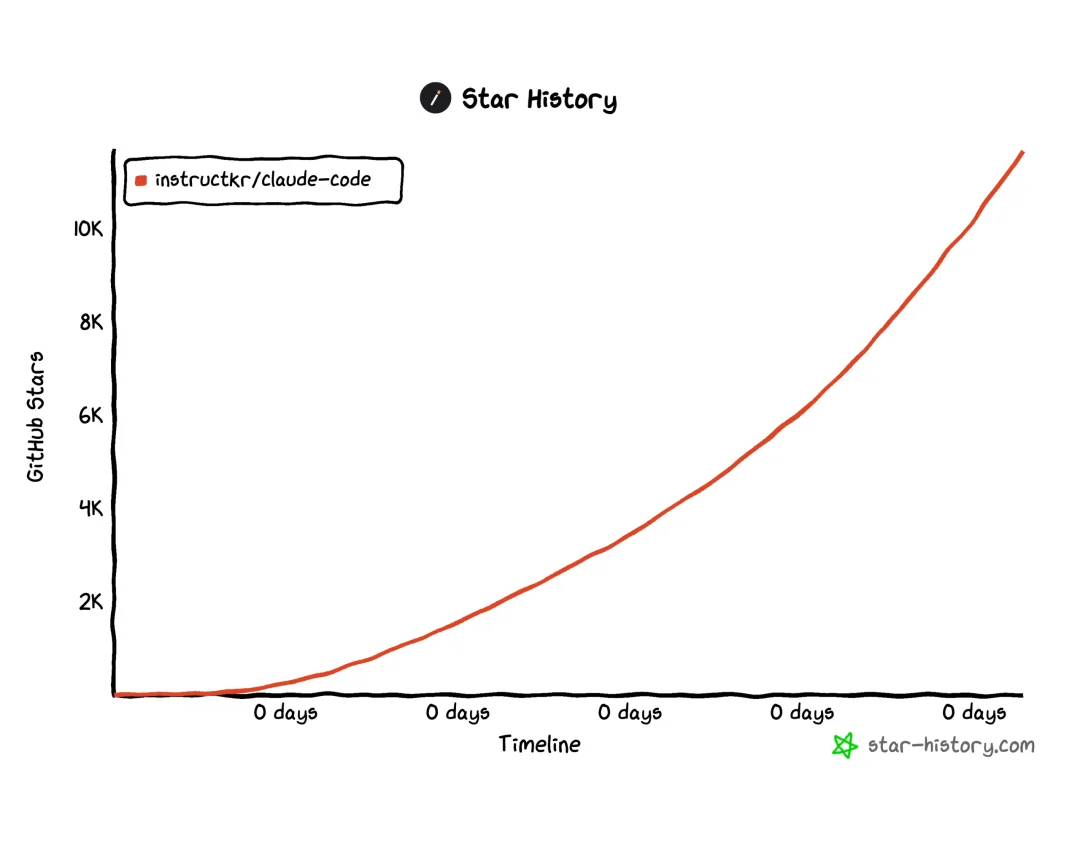
Star growth curve — crossed 10,000 stars within 60 minutes
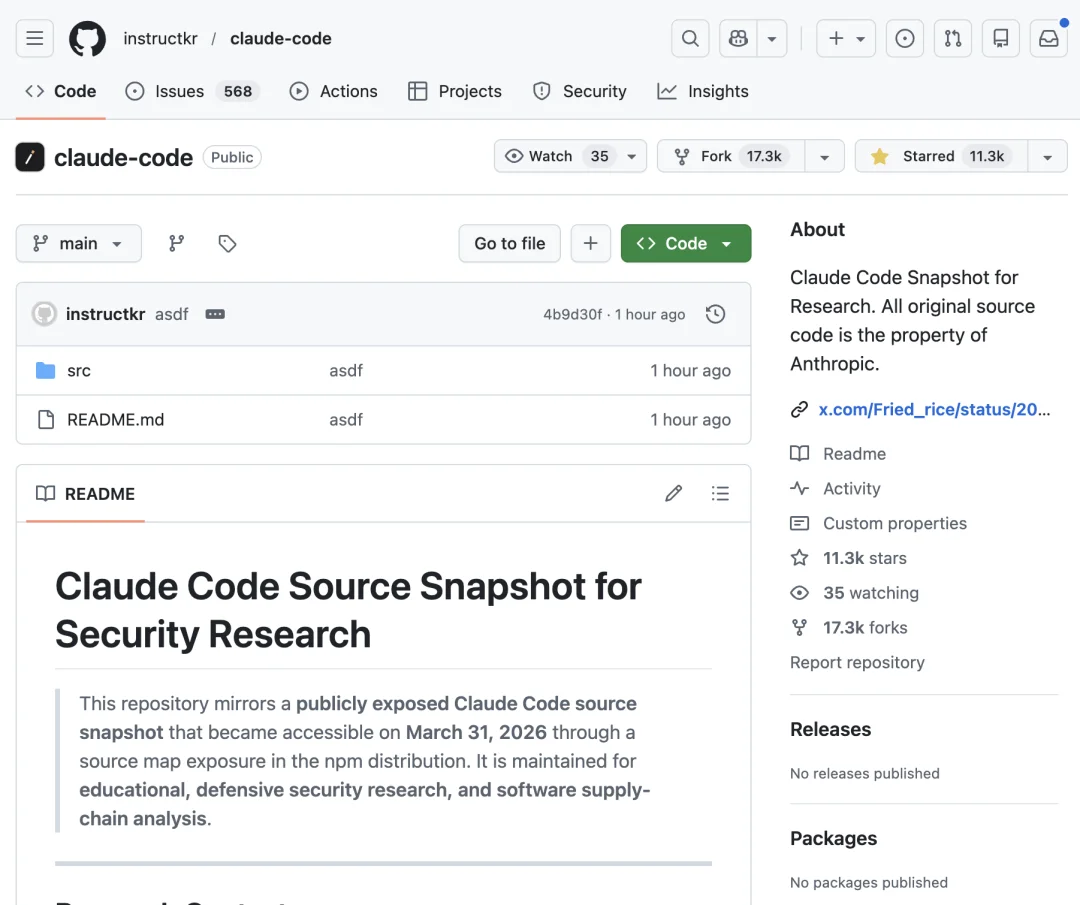
Repository metrics snapshot
Two Distinct npm Incidents — Not One
March 31 saw two unrelated supply-chain events on npm — often conflated but technically independent:
🔹 Incident 1: axios Supply-Chain Attack
- Attacker compromised maintainer
jasonsaayman’s npm account - Published malicious versions:
axios@1.14.1andaxios@0.30.4 - These versions injected
plain-crypto-js@4.2.1, which deployed a cross-platform RAT (macOS/Windows/Linux) - Attack timeline was highly orchestrated — clean
plain-crypto-js@4.2.0→ poisoned4.2.1→ poisonedaxiosreleases within ~1 hour - Removed from npm after ~2–3 hours
🔹 Incident 2: Claude Code Source Leak
- No compromise or malware involved — purely a configuration oversight
- Caused by failure to exclude source maps in
.npmignoreor disable them in Bun’s build config - Unrelated to
axiosincident — same day, same registry, different root cause
💡 Same day, same platform — one attacked, one accidentally exposed.
How It Happened: Source Maps Gone Public
Source map files (.map) are debugging aids that map minified/compiled output back to original source — and often embed raw source via the sourcesContent field.
✅ Normal practice: Exclude .map files from npm packages using .npmignore or build-time flags
❌ What happened: Bun’s default behavior generated and included the full source map — no cleanup step applied
Result: A single 59.8 MB .map file acted as a complete, downloadable source archive.
Source file listing revealed in the leaked map
Inside the Codebase: Key Architectural Insights
🧰 Tool System: 40+ Permission-Gated Tools
Located in /tools/, each tool defines:
– Input schema
– Risk level (low/medium/high)
– Execution logic & sandbox constraints
Permissions model includes four modes:
– default: Interactive user confirmation per action
– auto: ML-based auto-approval
– bypass: Skip checks (for trusted contexts)
– yolo: Explicitly reject all actions
Core tools include: file I/O, shell execution (sandboxed), web scraping, Jupyter integration, LSP communication, and MCP resource access.
🔍 Query Engine: 46,000-Line LLM Orchestration Core
Housed in /query/, this is the largest module — responsible for:
– All LLM API calls & streaming
– Prompt caching (split into static/dynamic segments)
– Response validation & retry logic
Notable function: DANGEROUS_uncachedSystemPromptSection() — a self-documenting warning of past prompt injection pitfalls.
💤 Dream Memory System: “Claude’s Dreaming”
In /services/autoDream/, the autoDream engine runs background memory consolidation when:
– ≥24 hours since last run
– ≥5 sessions completed
– Exclusive lock acquired
Process: reads logs → extracts new insights → merges/refines memory → trims to ≤200 lines
Prompt used: “You are dreaming — reflectively consolidate memories for future recall.”
⚙️ KAIROS Mode: Always-On Background Assistant
Hidden in /assistant/, KAIROS enables autonomous, event-driven operation:
– Runs continuously without user input
– Logs every observation, decision, and action in append-only daily files
– Enforces 15-second blocking budget: actions risking workflow interruption are deferred
– Exclusive tools: SendUserFile, PushNotification, SubscribePR
🤖 Coordinator Mode: Multi-Agent Orchestration
Under /coordinator/, transforms Claude Code from single-agent CLI into a dispatcher managing concurrent agents:
1. Research: Parallel codebase analysis
2. Synthesis: Plan formulation from findings
3. Implementation: Code edits + Git commits
4. Verification: Validation of correctness
Rule embedded in coordinator prompt: “Don’t say ‘based on your findings’ — read the actual findings, then specify exactly what to do.”
☁️ ULTRAPLAN: Remote Heavy-Lifting Mode
Offloads complex planning to cloud containers running Opus 4.6, with:
– Up to 30 minutes of remote reasoning time
– Local terminal polls results every 3 seconds
– Real-time browser UI for approval & visualization
🐾 Buddy: Terminal-Based Tamagotchi
In /buddy/, a deterministic ASCII pet system:
– Seeded via userId hash → Mulberry32 PRNG
– 18 species across 5 rarity tiers (1% legendary, 1% shiny)
– 5 attributes (DEBUGGING, PATIENCE, CHAOS, WISDOM, SNARK) rendered as animated ASCII glyphs beside the prompt
– Scheduled for official launch in May 2026
🕵️ Undercover Mode: Internal Developer Safeguard
Defined in /utils/undercover.ts, activates when internal repo detection is ambiguous:
– Strips internal identifiers from commit messages & PR descriptions:
– Model codenames (Capybara, Tengu, Fennec)
– Unreleased version strings
– Project names (Claude Code)
– Comment states: “If uncertain whether internal, stay undercover.”
Additional Revelations
| Category | Detail |
|---|---|
| Internal Codename | Tengu — used across feature flags (tengu_*) and configs |
| Fast Mode Alias | Penguin Mode — visible in API endpoint: claude_code_penguin_mode |
| Computer Use Codename | Chicago — implemented via @ant/computer-use-mcp, gated to Max/Pro users |
| Beta Headers | redact-thinking, afk-mode, advisor-tool — unreleased client-side controls |
| Client Auth | Every request includes x-anthropic-billing-header to verify official installation |
Timeline: Five Days, Two Breaches
| Date | Event |
|---|---|
| Mar 26 | Anthropic CMS misconfiguration exposes ~3,000 unpublished assets — including draft blog on Claude Mythos (codename Capybara) and EU CEO event details |
| Mar 30, 05:57 UTC | Clean plain-crypto-js@4.2.0 published (trust-establishment phase) |
| Mar 30, 23:59 UTC | Malicious plain-crypto-js@4.2.1 released |
| Mar 31, 00:21 UTC | Poisoned axios@1.14.1 published |
| Mar 31, 01:00 UTC | Poisoned axios@0.30.4 published |
| Mar 31, ~03:15 UTC | Malicious axios versions removed from npm |
| Mar 31, daytime UTC | Chaofan Shou discovers @anthropic-ai/claude-code v2.1.88 contains full source map |
| Mar 31, <1hr | instructkr/claude-code hits 11,000+ stars & 17,000+ forks |
⚠️ Both incidents were configuration failures — not breaches involving hacking or insider threat.
Repository Structure Overview
claude-code/
├── assistant/ # KAIROS persistent assistant
├── bridge/ # IDE integrations (VS Code / JetBrains)
├── buddy/ # ASCII pet engine
├── commands/ # ~50 slash commands
├── components/ # ~140 React terminal UI components
├── coordinator/ # Multi-agent orchestration system
├── memdir/ # Persistent memory storage
├── plugins/ # Plugin framework
├── query/ # 46K-line LLM query engine (largest module)
├── services/ # Backend services (incl. autoDream)
├── skills/ # User-defined skill definitions
├── tools/ # 40+ permission-scoped tools
├── utils/ # Utilities (incl. undercover.ts)
├── voice/ # Speech input stack
├── main.tsx # Entry point (785 KB)
├── QueryEngine.ts # Core query orchestrator
└── Tool.ts # Base tool class (29K lines)
Current Status
As of publication, Anthropic has not issued an official statement regarding the source code leak. The company previously attributed the March 26 CMS incident to “human error in external CMS tool configuration.”
📢 “Oh no — someone cloned it!”
— Anonymous developer reaction, widely shared across engineering communities
Article originally published by “Cyber Zen Heart”, author “Golden Legend Smart Guy.”